The Liquidity Framework
Targeting the Multi-Billion-Dollar Infrastructure behind 21st Century Threat Finance
Illicit finance is no longer episodic crime. It has matured into shadow liquidity systems: parallel infrastructures where state actors, cartels, mercenary groups, and cybercriminals pool and regenerate capital. These systems – empowered by digital currencies and vast capital outflows – function as underground financial institutions, enabling adversaries to outlast sanctions, rebuild after seizures, and finance operations at scale.
Global institutions still treat illicit finance as a series of anomalies — bad transactions, rogue exchanges, isolated scams. This fragmented view leaves the circulatory system itself untouched. The result: adversaries adapt faster than regulators, and global security erodes while enforcement chases symptoms.
Why It Matters
National Security: Shadow liquidity sustains proxy wars, sanctions evasion, cyber operations, and militant logistics. It is the bloodstream of hybrid conflict.
Economic Integrity: These systems siphon billions from households and corporations alike. They play a destabilizing role in across whole regions, as witnessed recently in Southeast Asia.
Beyond Control: These systems feed off capital outflows (especially from China) but answer to no one — even the countries that spawned them.
Real World Threats: Iran-backed proxies and Southeast Asian militant groups use these networks. So do multi-billion-dollar global scam operations. The threat is real and it’s already here.
Strategic Leverage: Whoever maps and disrupts these infrastructures doesn’t just fight crime — they control adversaries’ capacity to project power.
The Gap
Tools are reactive: Blockchain analytics, anti-money laundering (AML) compliance, and sanctions designations find anomalies but not architectures.
Regulation is fragmented: National silos and outdated legal frameworks make systemic action impossible.
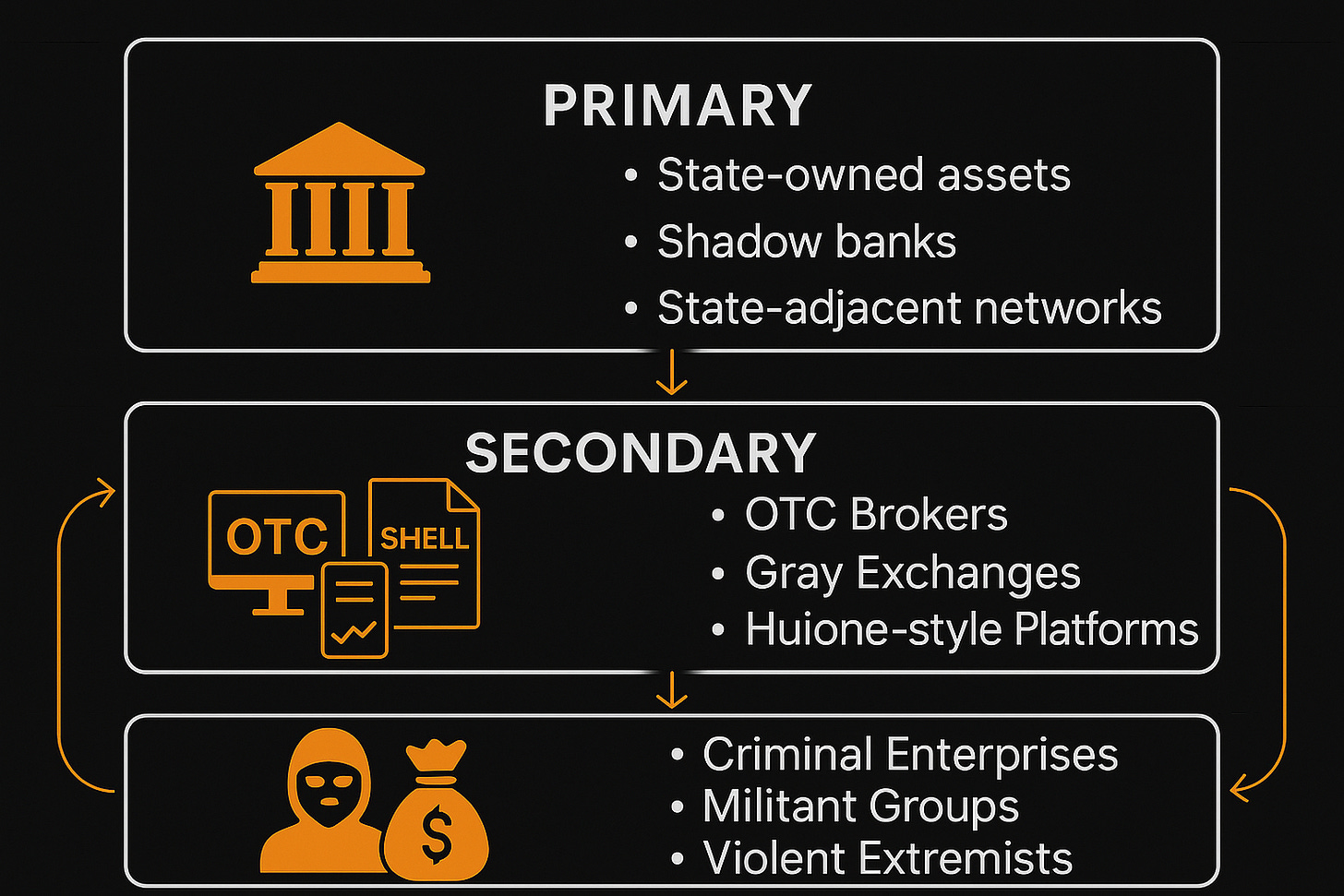
The BTL Framework
Between the Lines Research has developed a framework to analyze illicit finance as infrastructure rather than incident. Key components:
Primary Liquidity: Capital outflows — fast, mobile fuel.
Secondary Liquidity: Informal systems (hawala, OTC desks, trade credit) that enable gray exchange.
Tertiary Liquidity: Long-term reservoirs (real estate, commodities, criminal operations [ex: scam centers], militant/ terrorist groups) that can be mobilized in crisis.
By tracking conversion between these tiers, we expose the stress points adversaries use to survive and regenerate.
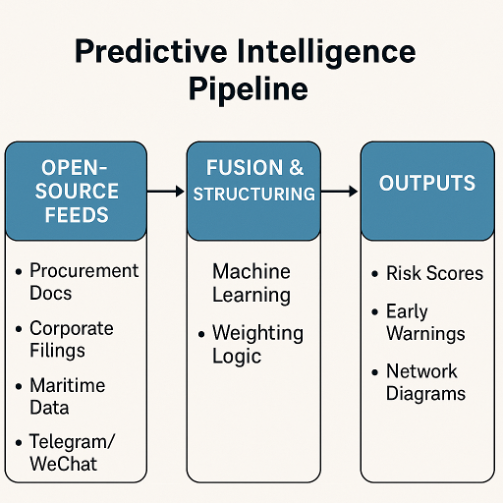
Between the Lines’ proprietary Three-Tiered Framework and Predictive Intelligence Pipeline
Applications
National Security: Identify and pre-empt liquidity corridors sustaining adversary militaries and proxies.
Financial Sector: Develop financial intelligence (FININT) products that move beyond anomaly detection into systemic mapping.
Tech & Cyber: Integrate liquidity mapping with cyber threat intel to close the gap between digital intrusions and financial outcomes.
Case Study: Chinese Capital Outflows and Scam-Backed Militias
The rapid outflow of Chinese capital, driven by elite flight and tightening domestic controls, has created offshore liquidity pools across Southeast Asia. These flows illustrate how shadow liquidity systems evolve from simple capital escape into infrastructures that finance armed groups and destabilize regional economies.
Capital Outflows (Primary): Wealthy elites and mid-tier operators move funds offshore to evade Beijing’s capital controls. Much of this first moves through cash, stablecoins, and front companies in border economies.
Infrastructure Formation (Secondary): These outflows feed into OTC desks, casinos, and unregulated payment processors, which become regional hubs for laundering and reinvestment for tertiary actors.
Tertiary Parasitism and Destabilization: At the highest tier, the threat becomes acute.
Scam compounds siphon billions annually through trafficked labor.
Armed groups and private militias provide protection for these hubs, turning them into semi-sovereign enclaves in Cambodia and Myanmar.
Platforms like Huione facilitate laundering at scale, enabling actors such as the Houthis to exploit the same corridors.
The fact that Huione remains active despite sanctions and a nominal shutdown shows that these systems are networked, not episodic — requiring a systemic approach.
This cycle shows how a single driver — Chinese capital flight — cascades into a shadow liquidity architecture that finances militancy, erodes sovereignty, and extracts value from legitimate economies. Episodic enforcement actions like sanctions strike at symptoms in the tertiary tier, but the real threat lies in the multi-tiered networks that remain resilient and regenerative.
What Between the Lines Provides
Between the Lines translates this framework into actionable outputs: tailored briefings, case studies, and strategic advisory designed to help institutions understand and anticipate how shadow liquidity shapes their risk environment. Whether the need is regulatory foresight, adversary mapping, or integration into existing threat intelligence, BTL brings the concepts down to ground level — where they can guide decisions, not just analysis.